The Role of Cloud Computing for Business
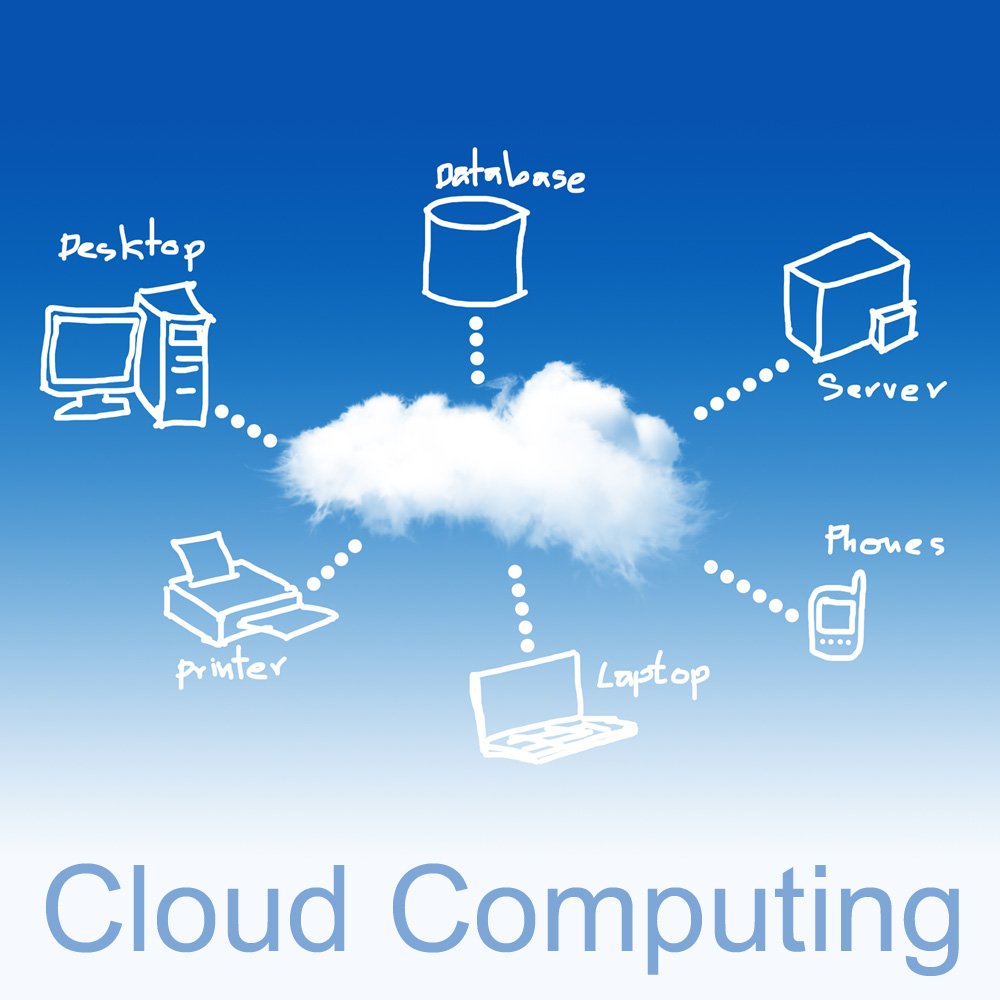
Nowadays, the internet and technology have improved the performance and performance ranges in companies of all sizes. Increased internet utilization and statistics costs of speed, in conjunction with an expansion of the electronic system and larger storage capacities, have introduced new technology in social media abilities. Cloud computing may be taken into consideration as the innovation of this new generation. These technologies have the potential to deliver a selection of advantages and specific things to an enterprise.
What Exactly Is Cloud Computing?
What precisely is it? Through a carrier provider, cloud computing is a machine that serves as an internet-based data center wherein customers can access documents and software programs accurately through numerous unique gadgets anywhere there’s internet access. It is an answer for groups and individuals looking for a clean manner to shop and access media from one device to any other, and the potential to share that media with other people who have been given access.
Role in Business
• The cloud computing community can also seem complex. However, it can be utilized by all of us. It isn’t always vital for the user to realize the headaches of the facilities involved, or the social press machine, and how it works.
• The exciting and suitable example for contrast would be electricity, wherein clients have access to the help but don’t always understand the systems and the things that provide the service.
• It can be used to keep an offline replica of critical records and as an internet-based backup. This will help in the case of file healing and computer maintenance.
• Since cloud computing companies supply IT infrastructures and corporate online commercial enterprise programs, these services can be utilized by investing little resources. This facilitates a lot to accumulate small-scale and medium-sized businesses in the global gift market.
• It could be personalized according to the desires of the commercial enterprise. It can prevent freelancing from covering worker expenses. The cloud computing carrier issuer gives an IT guide to the corporation, and they will not worry about anything.
When corporations use cloud computing, they have the assets they need to grow and boost their business online without having the costs and time to replace. When looking at all the commercial enterprises collectively together with your cloud, it is clear why cloud computing is becoming the choice for corporations all over the globe. When searching for a number on your website, consider the employer benefits of using the cloud.
How Effective Are Home Security Cameras at Deterring Burglars?

You will often hear cynics say that home security digicam systems are remarkable for recording crime; however, they do little to save you from it. Even if this had been true, registering against the law isn’t this sort of lousy issue, is it? The police have a much better hazard of finding and convicting housebreakers if they have photos of the incident. This is, in particular, useful if the cameras document clear mug shots of the crook(s). Although most oldsters would pick it if their security investment, in reality, avoided crime rather than record it. So simply, how powerful are domestic protection cameras as a burglar deterrent?
What the Research Says
There has been some tremendous research into this. One survey entitled, ‘Understanding Decisions to Burglarize from the Offender’s Perspective,’ is worth noting. The critical recognition was to investigate the minds of serial housebreakers, male and female, to determine how they make their choices. The purpose of this sixty-four-page study is to decide the following:
Despite what the cynics suppose, most intruders do take the presence of protection deterrents into consideration-cameras, alarms, dogs, and so on. This isn’t a hypothesis; however, the words from over four hundred reoffending burglars. Around 83% might look at the security scenario of a property earlier than making their decision. In different phrases, if safety is vulnerable or non-existent, they’re much more likely to break in. If safety features appear robust and powerful, they’re much more likely to transport directly to a more superficial location. In quick, the opportunistic burglar cherry-picks their target property primarily based on its security, or lack thereof.