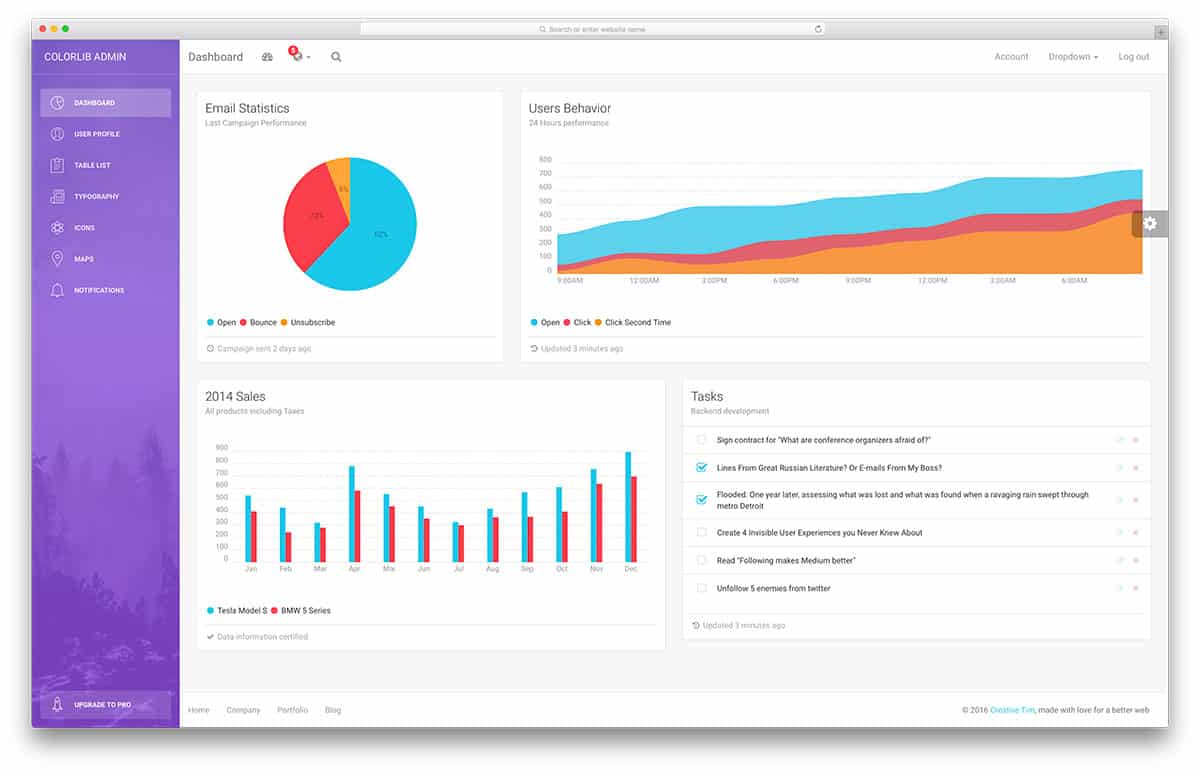
Why You Should Avoid Using A Free Template
You would have probably been informed to use an eBay template, and the importance of it is. It is considered an easy, reliable, and reasonably-priced way of growing sales. There are two sorts of templates, paid and free. But you need to behave cautiously and choose accurately.
Generally, templates that you find for free are of terribly low quality. And why is that? Because no good clothier could provide their challenging work and creativity to you for free. You need to by no means consider the usage of a ufreetemplate because of the following.
The best of loose templates is regularly compromised. They do not meet the standards of a good template.
Free templates frequently have attached hidden links in them. This applies to all net templates and not simply this.
You may not have backup help. So if something goes wrong, you are responsible for fixing it.
The unfastened template might, of course, not have all of the proper codings as the designer would not put sufficient effort into it; hence, using it might result in your own loss.
A template with a beautiful design could cost you loads less than what you suspect. And the blessings you get in return for that small sum of money you pay are exceptional.
The templates built by a perfect designer could have complex paintings placed into them and might convey an experience of professionalism. The feel of professionalism would help entice purchase site visitors towards you.
As you will be hiring someone to construct your template for you, you can place a private essence into your shop. Meaning you can customize it without problems.
Your eBay template, as built in this manner, could have its very own separate identity. This is one of the factors that help construct belief among your clients; this belief forces them to return to your shop to store time and again, increasing sales.
Another available option is a customized template. Everything in that template is a custom construct. This issue requires an excessive level of professionalism in choosing that store.
A company that gives off a feel of professionalism shows the customer how capable you are, and this builds consideration. This is accepted as accurate, forcing them to revisit your save and buy gadgets. The revisiting facilitates astonishing remarks attracting increasingly more people closer to your rescue.
This enables you to increase your business and increase your sales. The templates available at no cost would possibly seem a clean approach at the time; however, they could prove to be complicated in the long run. Not only could they persuade you to spend your money on them in a while, but it would also be a total waste of time.
So it’s miles better to spend a bit of money ahead and get an excellent, high-quality dressmaker who builds the template that might save time and money in the end and help you grow your income.
And in case you want something incredibly outrageous, you could have a customized template constructed for you.
Car Theft Solved by Private Investigators

From time to time, a private investigator is probably requested to track down a missing car. A car can be stolen from a public location, an individual’s house, or a car condominium employer.
Types of Car Thefts:
During economically challenging instances, car thefts increase. Some humans try to steal motors from rental businesses via fake IDs to lease vehicles, after which they genuinely never go back to them. Some spouse borrows cars for their use, whether for regular daily use or for transporting contraband and later abandonment. Some turn the stolen motors over to cut stores, where the cars could be used for elements. Some need an automobile to take on a race or joyride and could abandon the car after using it for some time.
Some will promote a stolen automobile to an unsuspecting character who has no concept that they simply bought a stolen car. Sometimes, the owner offered the car in excellent faith to someone who exceeded a terrible cheque. In different cases, a pair may additionally have surrendered their 2d car to a releasing company to cut down on costs, but the vehicle might also have been leased to a “customer” who disappeared. Thefts may be for comfort – the thief can also have a few stolen goods to move.
No need to elaborate on the motive for the theft; it is as much as the private investigator to apply their ingenuity to discern what happened and tune down the auto. It’s always an excellent idea to report a police file first; however, because the police might not be able to make an effort to write down your car, an excellent Private Investigator can be available at a moment’s notice