iOS VS Android
Mobile OS:
A cellular operating system, also referred to as a mobile OS, is a software application specifically designed to run on cell gadgets, including cellular phones, smartphones, PDAs, tablet computers, and other handheld devices. The cell running system is the software platform that includes essential software, Middleware, and working devices that run on cellular devices.
Mobile working device kinds:
Symbian OS (Nokia)
Bada (Samsung Electronics)
BlackBerry OS (Research In Motion)
Palm OS (Garnet OS)
Windows Mobile (Windows Phone 7)
Android OS (Google Inc.)
iPhone OS / iOS (Apple)
Among some of these Mobile OS, of them are very famous.
IOS
Android
We identified a few not-unusual distinctions between these two Mobile OS.
IOS:
iOS is a platform that has a few restrictive hints. As iOS isn’t always open source, the equipment is restricted and fixed to improve the iOS apps. Nothing is from the outside, and I simply had to comply with what was given in the rule. In this manner, iOS isn’t always too flexible. The reason behind this is that iOS does not compromise on security. The tradeoff of the software improvement argues that we need to compromise one of the constraints of availability and safety. So the iOS plate shape is confined, and there is nothing profound for the development. There isn’t any malware assault in iOS. The possibility of information loss is 50%. iOS no longer provides unlimited access control to its users. Appreciation for the play takes several instances. There are many regulations when uploading an app to play Keep. Ninety percent of OS devices run on the present-day updates of iOS. Paid apps are available in 155 nations. IOS apps are developed in Objective-C or Swift.
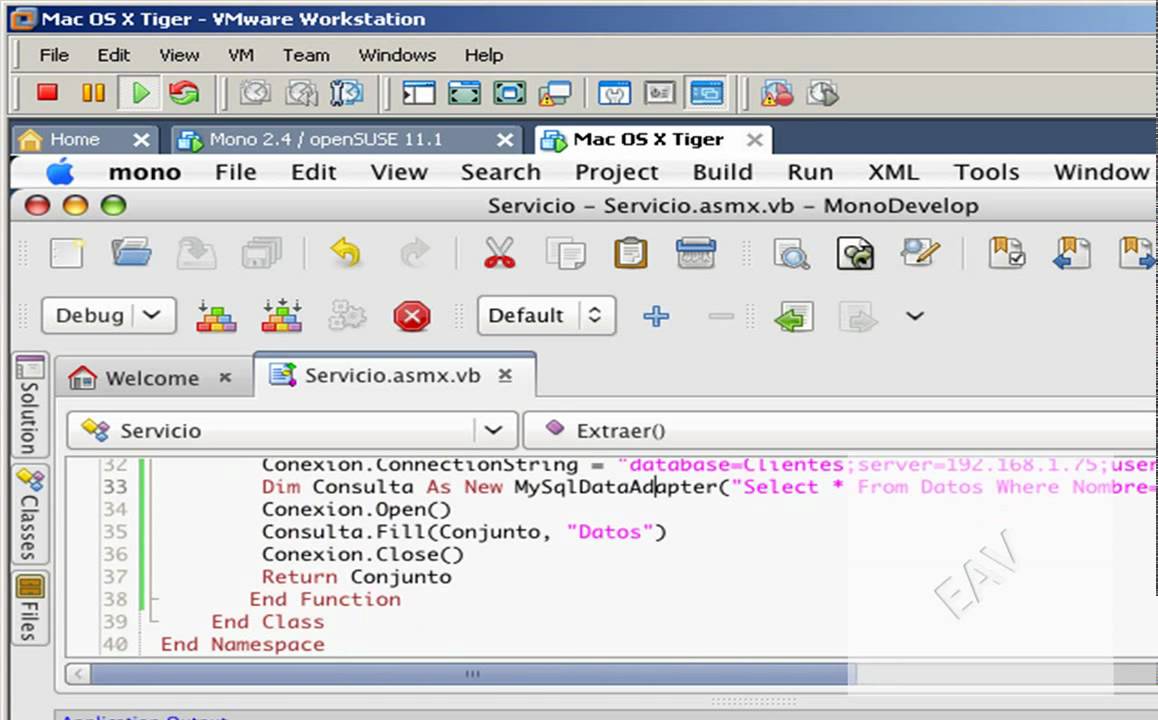
Android:
Android is a platform that includes three layers: the running gadget, the core layer, and the application. Android isn’t only the OS. But it’s far from the combination of those three layers. Android is so flexible, as it permits 0.33 parties tools. It is because Android is an open-source platform. Android can compromise security. Malware can, without problems, attack information in Android. The possibility of record loss is 75%. It gives full access and manipulation to the users. Approval of apps for play save may be very short, within 6 to 8 hours. The guideline is flexible for play keepers. Zero .. 4% runs the contemporary version of Android. Paid apps are available in 132 countries. Android apps are developed in Java.
Microsoft Phone Call Fraud. What to Do and What Actions to Take

For a few years now. People of all walks of life, broadly speaking, people at home have been hit by Microsoft Phone Call Scams claiming that they work for Microsoft, while mentioning statements that include “Your license key code is wrong” or “Your Windows Computer needs to be updated”. Whilst those statements can be true. It is also a fact that Microsoft truely does no longer name any person who is walking a Microsoft license about this kind of factor.